Horizon Monitor puts the world’s open data at your fingertips.

Name, Define, and Monitor Alert
Marker 2Choose data sources and dates
Marker 3Visualize alert data to identify trends and context
Marker 4Review alert summaries
features
Horizon Monitor gives you the power to:

Access complete data
You no longer have to rely on someone else’s metadata. You’re the expert and deserve to have every piece of social media intelligence at your fingertips – screenshots, raw artifacts, etc.

Customize your situational awareness
Easily customize the breadth and scope of your social media monitoring to ensure you’re getting alerts for the most relevant information for your case. You pick the source – forums, chat services, social media, DarkNet, TOR, etc.


Access historical data
The internet moves at warp speed. If you’re manually gathering data, you don’t have access to crucial historical social media information that may be the key to closing down a threat. With Horizon Monitor, access our historical archive from 2011 to today.

Extend your reach
Our stuff works with your stuff. Open APIs and integrations make it easy. Scalable automation means you can broaden your scope and reach of your social media investigations for real time situational awareness.

Horizon Monitor is changing social media investigations for the world’s best law enforcement and security organizations.
Physical Security/
Predicting Violence
Clever security teams use Horizon Monitor in their investigation to find indicators of unrest and violence before they start. Because riots don’t start in a vacuum; there are always indicators.
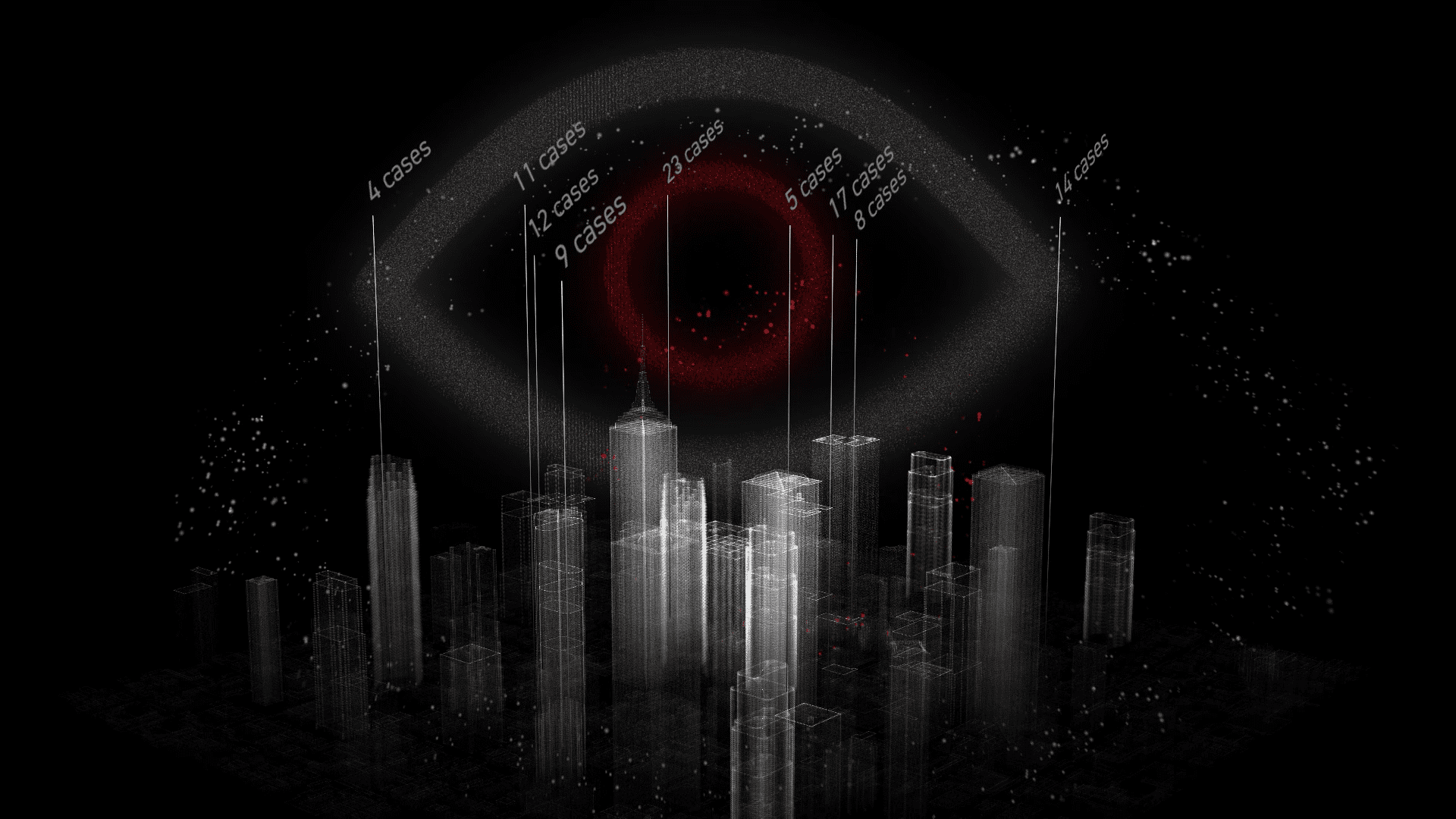
Public Safety / Opiod Crisis
If you can identify opioid sales and overdose hotspots, you can direct life-saving therapies and support to those areas. Horizon Monitor’s tailored monitoring and alerting is being used by public health and safety organizations to save lives.
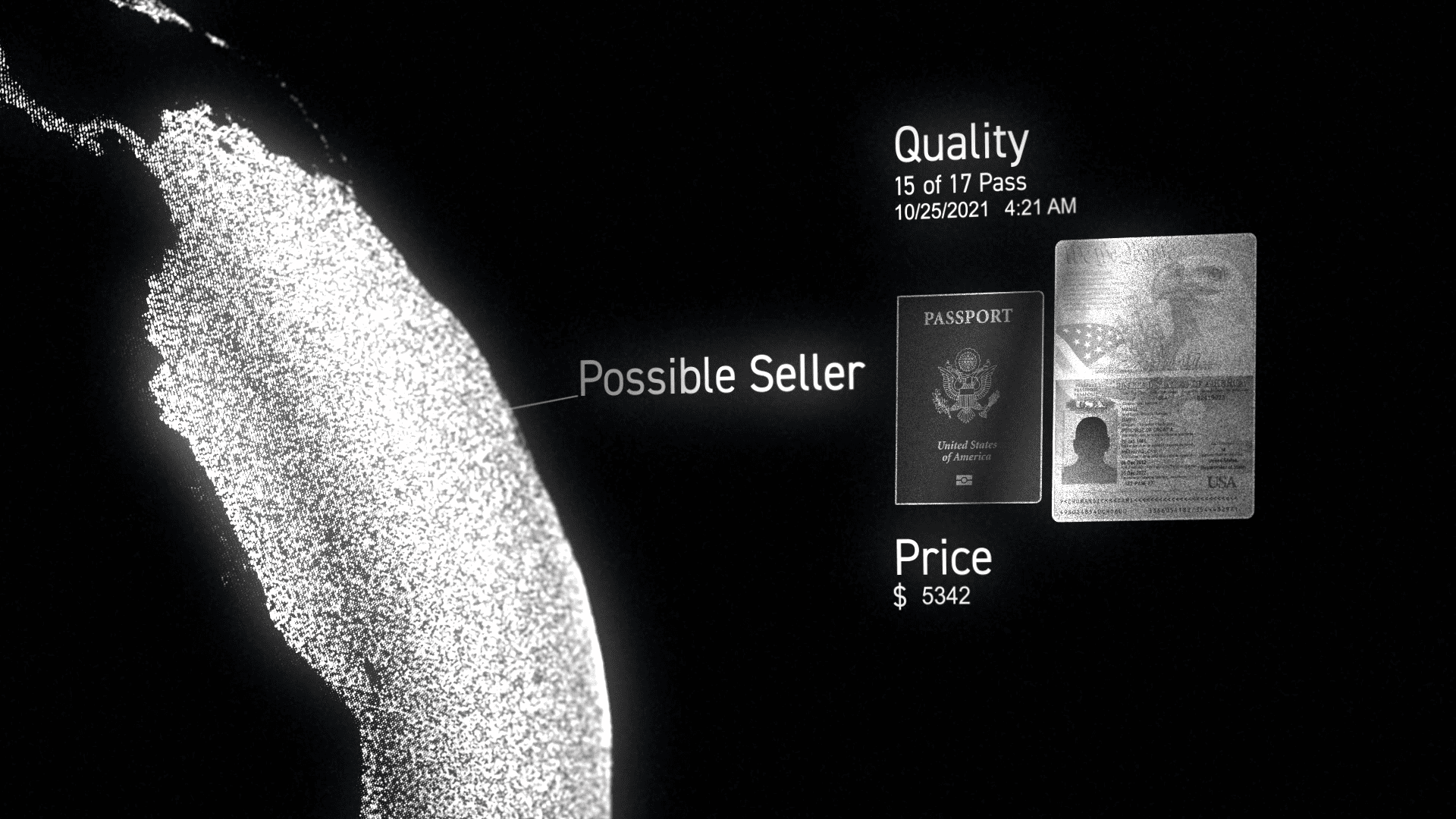
Law Enforcement / Fraudulent Documents
Criminals buy counterfeit documents like passports and other identification online. Horizon Monitor allows law enforcement social media investigation teams to track sales and gather data on potential use, ultimately stopping criminals from using them.




Bring the world's
data to you.
When it’s your responsibility to identify and stop threats, you don’t have time to collect and search across the world’s open data and social networks. Horizon Monitor lets you broaden your scope and monitor on your terms on social media — being alerted to relevant keywords so you can identify threats before they become problems.
INVESTIGATE ON THE GO - ANYWHERE, ANYTIME
Use OSINT, breach data, intelligence, monitoring and geolocation analysis to take investigations further in one comprehensive platform. Our OSINT tool helps you uncover valuable insights and make informed decisions.
ELEVATE YOUR INVESTIGATIONS NOW