Below, we compare 24 OSINT tools used by professionals for advanced intelligence gathering, with free and paid options.
| OSINT Tool | Best For | Pricing | Key Features |
|---|---|---|---|
| ShadowDragon | Comprehensive investigations | Paid |
Link analysisReal-time monitoringMalware analysis600+ data sources
|
| ExifTool | Metadata and file analysis | Free |
Metadata extractionGeolocation dataTimestamp verificationMulti-format support
|
| DNSDumpster | Domain reconnaissance | Free |
DNS record mappingSubdomain discoveryIP identificationInfrastructure visualization
|
| VirusTotal | Malware and URL analysis | Freemium |
Multi-engine scanningDomain reputationWHOIS lookupPassive DNS
|
| Google Earth Pro | Geolocation and visual verification | Free |
Timeline sliderDistance measurementGIS data import3D terrain
|
| Recorded Future | Threat intelligence | Paid |
Real-time threat mappingPredictive analyticsDark web monitoringSIEM integration
|
| DeHashed | Breach monitoring | Freemium |
Leaked credential searchesReal-time monitoringAPI accessBreach detection
|
| SpiderFoot | Automation and OSINT collection | Free |
200+ modulesAPI integrationAutomated scanningThreat intelligence
|
| Google Dorks | Advanced search queries | Free |
Advanced operatorsExposed file discoveryVulnerability identificationTargeted searches
|
| Shodan | IoT and device discovery | Freemium |
Internet-connected device indexingVulnerability assessmentMetadata analysisPort scanning
|
| Censys | Attack surface visibility | Freemium |
Asset discoveryCertificate trackingNetwork configuration insightsAlerting
|
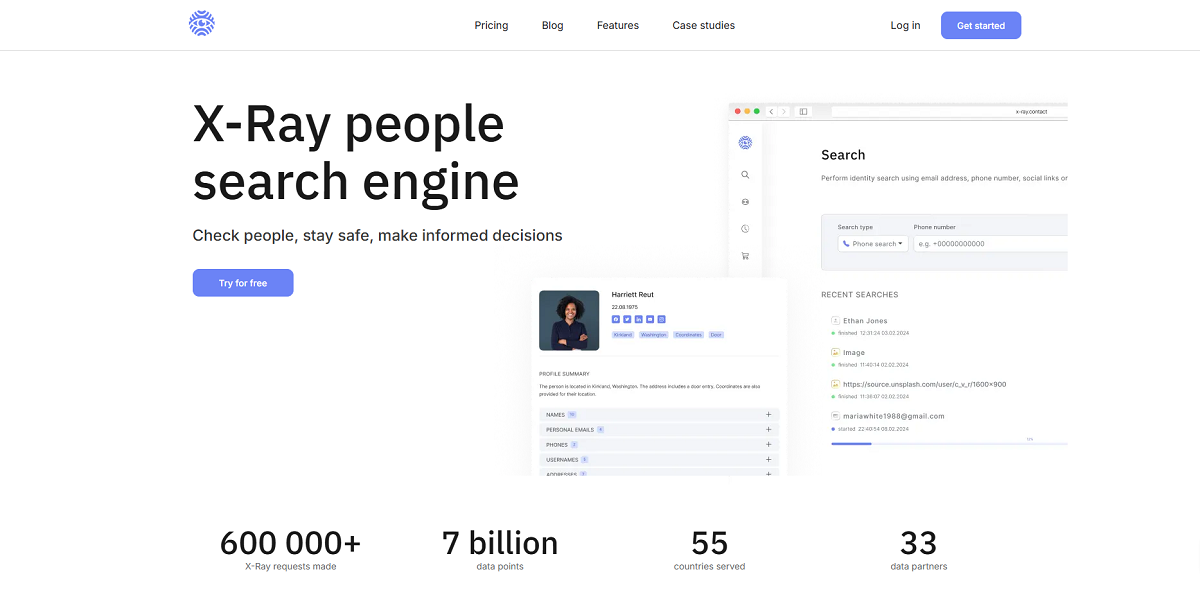
| X-Ray Contact | People identification | Freemium |
Email/phone lookupUsername correlationSocial media profilingImage search
|
| Espy IRBIS Pro | Background checks | Paid |
Multi-source aggregationRisk scoringAlias detectionDark web mentions
|
| DomainTools | Domain intelligence | Freemium |
DNS recordsDomain registration dataThreat actor mappingRisk scoring
|
| Meltwater | Media and social monitoring | Paid |
Social listeningSentiment analysisMedia intelligenceTrend tracking
|
| SecurityTrails | Historical DNS data | Freemium |
DNS historyIP trackingSSL certificate dataAPI access
|
| Spokeo | People search | Freemium |
Public recordsSocial media profilesContact infoEmployment history
|
| IntelTechniques | OSINT tools and training | Free |
Curated search toolsPrivacy-focused searchesMulti-platform queriesEducational resources
|
| Gephi | Network visualization | Free |
Interactive graphsRelationship analysis3D renderingClustering algorithms
|
| OSINT Framework | Tool directory | Free |
Categorized tool indexDirect linksTool metadataRegularly updated
|
| Recon-ng | Web reconnaissance | Free |
Modular architectureAPI integrationAutomation scriptingCustomizable workflows
|
| theHarvester | Email and subdomain gathering | Free |
Multi-source searchesEmail discoverySubdomain enumerationExport capabilities
|
| Feedly Threat Intelligence | Threat monitoring | Freemium |
AI-powered feedsCVE trackingSTIX formatAutomated summaries
|
 Nico Dekens – aka “Dutch OSINT Guy”
Nico Dekens – aka “Dutch OSINT Guy”